
Illustration: Mads Nordtvedt
In «the Da Vinci Code» the hero and heroine chase mysterious secrets; their quest requires them to crack one code after the other – from picture puzzles and mirror writing to messages hidden in paintings. Fans of today’s bestselling thrillers like the Da Vinci Code could be forgiven for believing that encryption’s main use is to help sinister brotherhoods guard secrets for centuries, even millennia. But a different, real-world brotherhood actually does use encryption– and their motivation is every bit as evil as that of their fictional counterparts. Cryptography is a dangerous and powerful weapon in the hands of criminals – and the codes have very little to do with picture puzzles and mirror writing.
HAIRY MESSAGES
Krypto is Greek for “hidden” or “secret”. Once upon a time a courier might have had a secret message tattooed into his skull. After a long wait for his hair to grow back, he would have finally been sent off with the message. These days we don’t have the luxury of waiting for haircuts to grow in, plus we have other methods that can be equally devious: we can exchange important information via digital means.
– But in one sense it’s really the same, says cryptologist Kristian Gjøsteen at NTNU. – If the cryptographer manages to camouflage the message so that criminals can’t distinguish the information from random noise on the web, the cryptographer has succeeded. The message has become so “hairy” that it is hidden from view.
CHILD’S PLAY
At a time when access to information is increasing at an ever faster pace, the great challenge is to create statistical tools for finding the exact information sought. The winners are those who manage to calibrate their search engines with sufficient accuracy to provide only the information that users want.
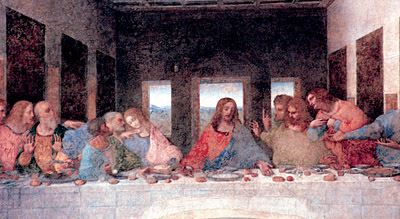
Leonardo da Vinci’s famous painting “The Last Supper” from 1498 is said to be hiding the key to
the riddle of the Holy Grail. This is the riddle that Dan Brown used as a basis for his thriller “the DaVinci Code”, but the encrypted texts in his book are child’s play, according to today’s cryptologists.
Foto: Antonio Calanni/AP/Scanpix
For the cryptographer, the challenge is exactly the opposite: Instead of providing easy access, the cryptographer’s job is to render the information as inaccessible and incomprehensible as possible.
After Dan Brown wrote his best seller about the hidden message in Da Vinci’s famous Last Supper, there has been an upsurge of interest in cryptography – which is good, says cryptologist Gjøsteen. He observes, however:
– Brown’s so-called encrypted texts are child’s play. They are frankly nothing to get excited about. But is it possible to encode a message in such a way that it cannot be decoded?
A MILLENNIUM’S WORTH OF PROTECTION
– The answer is yes. But that requires a key that is longer than your actual message, Gjøsteen responds.
Absolute protection is possible, then, but impractical – because how do you transmit the key to the receiver? Perhaps by encoding it with a new key. Which in turn needs to be transmitted… And so on. – Thus the conclusion was that one should settle for second best: a code capable of withstanding attacks for at least a millennium, even if the attack involves the heaviest computing power available, he explains.
A millennium should suffice. Surely that means that the task is next to impossible for the attacker?
– Not necessarily. A central question is whether the attacker depends on being able to read the whole message, or whether partial information is enough – such as the names of places or people. In some cases all you need to know is the identity of the receiver, says Gjøsteen.
THE LETTER “E”
TRY ENCRYPTION
Many programmes available on the Internet use advanced encryption. The following are just two examples of commonly available programmes:
ENCRYPTION OF E-MAIL The programme PGP (Pretty Good Privacy) allows you to encrypt e-mails and other computer files. If you send an encrypted e-mail to someone, the receiver needs the right key in order to decode and read your message.http://www.pgp.com
HIDDEN MESSAGE IN A PICTURE With the programme «Hide in Picture» you can try steganography. This allows you to hide a message in an ordinary image file.http://sourceforge.net/projects/hide-in-picture/
Modern decoding relies heavily on statistics. The simplest form of statistics is a frequency count of the letters of the alphabet – from which the letter “E” emerges as the one that crops up most often. If the key in question consistently translates E in the same way every time it occurs, and the message is of a certain length, the letter is easily decoded. The next step is to look for the letter that occurs most frequently in combination with E. Soon, the next letter is cracked. Then the snowball starts to roll.
Therefore, static encryption keys are out. – The key needs to be dynamic, so that E is not translated in the same way each time it occurs. A simple variation may be to pair letters with each other. Another method is to number the translations, for example from 1 to 10, so that the first and 11th times E crops up in the text, it looks the same, explains Gjøsteen. – Nonetheless, we are still talking about very simple codes, he adds.
So what are the major current challenges for cryptologists?
– The major challenge is probably proving that your data is sufficiently protected, Gjøsteen says. – How safe is the coded message? If it can withstand direct attacks, you may feel reasonably safe, especially because the basic precondition for a threat to materialise is always that the message has already been detected. That means before the attacker can make an attempt at decoding a message, he must have detected and identified that message in the first place.
INTERNET BANKING
The customers – those who need to send safe information – come in different shapes and sizes. Not surprisingly, the most traditional users of cryptography are the military, the secret police, and similar organisations. But according to Gjøsteen,we are currently experiencing a great increase in civilian use: banks, insurance companies, finance companies, mobile telephony and telecommunications companies all employ encrypted messages.
This writer has long been wondering how his online bank encoder works. The customers of my bank get a small calculator that generates a unique, eight-digit code each time the PIN code is entered. The code is recognised by the bank’s server, and can only be used once. How is this possible?
Gjøsteen emphasises that he does not know the security routines of my bank, but in principle, the method is simple. Two things are needed: a code key, and a dynamic factor – a counting device of some description or other. If the calculator has a time device, it is all very simple. Another, even simpler method is based merely on the number of times the calculator is used. – Usually, you only generate a new code each time you log on to conduct a transaction on the net. Therefore, the bank will register each code. All that is needed is to keep on counting, Gjøsteen says.
– This is not a matter of encryption, though, he clarifies, but of authentication,which constitutes a part of cryptography.
PROTECTION OF PRIVACY?
Today’s cryptography is a potent weapon in the hands of criminals. But modern encryption is emblematic of a classic dilemma in a more acute form: the individual’s right to privacy and legal protection versus the needs of the police to find out what criminals are up to. If our only concern was police needs, we could mount a CCTV security camera on every street corner and continuously monitor all digital traffic – but do we want the authorities to know everything, in principle, about us?
We want to the freedom to go about our own business without any interference. But at the same time we would rather the authorities knew the whereabouts of Osama bin Laden.
– This balancing of different considerations is never ending, says Gjøsteen: France used to have a general ban on the widespread use of encryption. Apparently, that changed when someone discovered that the Americans, in their battle against global terror, were monitoring French electronic traffic.
INVESTIGATORS AT NTNU
– There are powerful tools for encryption out there that are both generally available and fairly simple to use, according to André Årnes. Årnes is a research fellow at the «Centre for Quantifiable Service Quality in Communication Systems», one of the many centres of outstanding research at the Norwegian University of Science and Technology.
Årnes works on information security. At the moment, he is on leave from his job as a special investigator at the High Tech Crime Division of the Norwegian National Criminal Investigation Service (NCIS). The Centre was transferred from the National Authority for Investigation and Prosecution of Economic and Environmental Crime (ØKOKRIM) some time ago. The move is an indication that organised crime is increasing on an international scale. In these situations, encryption has a prominent place.
– The current encryption algorithms are so powerful and so easily available that it is very difficult to break through their defences, says Årnes.
– Does that mean that the police are powerless?
– No, but the police may have to use a variety of different techniques. If we can’t crack encrypted messages and network traffic, we can try to get our hands on passwords and keys, or we can try to find the computer at either end of the flow of information. The encrypted messages are often not encrypted while sitting in the computers of the senders and receivers. – All systems have their weak points, Årnes adds.
UNCOVERED BY SPEED
Thus it is important to be able to track down computers on the Internet. Many registers on the net are openly available, and active tracking can help locate a computer. One possible method is network trigonometry – cross tracking of PCs on the net. This method is still in its trial stages, and is the topic of a Master’s thesis in progress at NTNU’s Department of Telematics.
– The starting point is round trip time – the time it takes a message sent from the undercover detective to the criminal’s computer to generate an answer. Data communication on the Internet takes place at about two thirds of the speed of light. If such messages are sent to the same computer from different places, it is possible to define a limited area within which the computer is likely to be located. Even if the speed is not constant, this still constitutes a good instrument. The method is new and untried, but promising, says Årnes.
PAIRED KEYS
Who, then, are the criminals who apply sophisticated data tools? The police have concentrated a great deal of effort on computer criminals who use the Internet for paedophile networks or to attack other computers. Among the former, the active use of PCs to share photographs is widespread. According to Årnes, however, traditional crime syndicates are increasingly discovering the potential advantages associated with modern encryption of their communication with each other.
A particularly successful encryption tool is a programme called PGP – Pretty Good Privacy – which is based on public key cryptography, with public and private keys. The public key is shared by everyone in the network, whereas the private key is closely guarded by the individual. A message encrypted with a public key can only be decoded with the matching private key. The public key can be used to verify what is called a digital signature on the message, which can only be generated with the matching private key.
Thus, the system supports both safe communication of a message, and secure identification of the sender of the message. A message encrypted with a public key is illegible to anybody else except the receiver (who holds the matching private key).
– This means that new keys can be transmitted in the message encoded with the private key, safeguarding the sender’s ID. It also means that criminal networks can build a system of public/private algorithms that cannot easily be penetrated, explains Årnes.
MANIPULATED PICTURES
In addition to encryption, steganography and anonymisation also represent important challenges.
Steganography is a variety of encryption where information is hidden in something like a picture. Small bits of digital information are placed in a code string that translates into a picture on the screen, making it is impossible for the naked eye to distinguish a manipulated picture from its ordinary counterparts.
– We know that these kinds of tools are available for steganography, but we do not know how much they currently used, says Årnes.
Criminals seek anonymity. If they can work from an IP address that cannot be traced back to them, they have a head start. For example, Internet cafes and libraries are places where people can remain anonymous. Moreover, there are many technical opportunities for hiding both one’s identity and one’s whereabouts. Thus, says Årnes, Internet tracking experts are under a great deal of pressure.
NCIS NEED FOR RESEARCHERS
The National Crime Investigation Service wants to co-operate more closely with computer investigation and electronic tracking researchers. – Computer technology is moving forward at an accelerating pace, and criminals are finding new ways to abuse this technology, says Rune Fløisbonn, head of the High Tech Crime Division.
The National Crime Investigation Service has recently joined forces with Norwegian universities: The agency will henceforth contribute its expert knowledge to master’s and doctoral programmes related to its fields of expertise. Moreover, the NCIS has initiated a research project financed by the Research Council of Norway.
– We have already committed to working with research fellows and Master’s students from NTNU and the University of Oslo, reports Fløisbonn.
By Tore Oksholen
The post Encrypted crimes appeared first on Geminiresearchnews.com.
